Conversation About the Recent Cyberattack
By: Cafo Boga, CPA, MDY

A frequent contributor in Illyria newspaper, Mr. Boga has authored numerous studies, essays, and articles on Albania, Montenegro, Kosova and the wider Balkans context. He has a Master in Degree in International Relations and Diplomacy from Norwich University.
He is also Chairman of the Albanian America Cultural Foundation, in New York.
A relatively small country, Albania is endowed with geography and natural resources that any country would envy, from an amazing coastline replete with beautiful beaches and crystal-clear waters to the magnificent Alps in the north, which seem to touch the sky. Albania is also blessed with a mild Mediterranean climate that varies according to topography. Being one of the oldest civilizations in the Balkans, Albania has many archeological sites and old stone castles that were built during different historical periods, as well as modern cities with developed infrastructure and a culinary industry that has become the talk of Europe. The people of Albania are hospitable and eager to please; they don’t consider tourists to be simply visitors but invited guests who are welcomed into their homes.
However, Albania is not without some serious problems, ranging from political to economic, social, migratory, and the list goes on. For 30 years, Albania has been trying to establish a western-style democratic system—but with limited success. Pervasive corruption has hampered Albania’s ability to break from the past and embrace the opportunity to build a better future.
Faik Konica, ambassador to the United States (1929–1939), writer, and statesman said, “If Albania were to ever die, then its epitaph should read: ‘Albania was born of God, saved by chance, died of politicians.’” He also said that “The enemy of the Albanian is the Albanian himself.” Almost a century later, those words hold true today. Albania’s political elite, who grabbed power following the collapse of the communist system, refuse to let go; they have become the ruling oligarchy. Omnipresent corruption has bled the economy and has hindered direct foreign investments. Despite all the good things endowed by God, including plentiful natural resources, the country remains relatively poor. Almost one-third of the population has left the country to seek better opportunities elsewhere in Europe and the United States. For those who remain in the country, morale is low; they are losing faith in their country’s political system, which seems to be losing its grip on democracy.
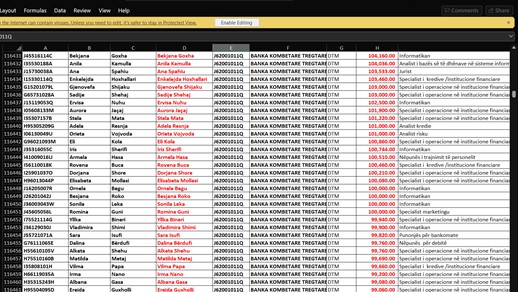
A recent, dramatic development within Albania’s Democratic Party, involving a quarrel between its two leaders as to who would be in charge, more closely resembles a fictional satire than a political reality. This week another thriller appeared on the scene: apparently the result of a cyberattack, someone posted personal records from a government database of state and private employees, containing the personal identity card numbers, employment, and salary data of some 637,000 people became public and was widely shared through social media, which sent a shockwave across the country and raised a lot of eyebrows. Prime Minister Edi Rama said the leak is being investigated. “According to a preliminary analysis, it looks more like an internal infiltration rather than an outside…cyberattack,” Rama told a press conference.
Notwithstanding the prime minister downplaying the incident, the information that somehow leaked to the public created a huge uproar because it revealed enormous anomalies in remuneration among public figures that cannot be logically explained. It appears that media and TV personalities are among the highest paid individuals in Albania, getting salaries that are not commensurate with what they do, and even higher in comparison to their colleagues in developing countries. The information hacked raises many questions that beg answers: Why are certain individuals’ remuneration so high? Why are some employed where they are? What services do they provide other than what is obvious? Is there some criminal activity involved, such as money laundering, corruption, or worse?
For the past few days, talk show hosts have invited local “experts” to shed some light on this incident by discussing what has transpired, who is to be blamed, and who is responsible for keeping confidential information safe. They all seem jittery, and for a good reason: undoubtedly the hacked data will have profound consequences, specifically in highlighting corruption in Albania. It is almost amusing to watch heated exchanges between participants on these shows, how they jump at each other like fish out of water.
Talking about fish brings to mind the former United States Ambassador to Albania, Donald Lu. On the issue of fighting corruption, he told the Albanian public to expect the arrest of political “big fish.” Time went by and no “big fish” were ever arrested because the ambassador’s promise had one fundamental flaw: the “big fish” are the governmental officials; how could he expect they would arrest themselves? The new United States Ambassador to Albania, Yuri Kim, has called on all authorities to increase their efforts in the fight against corruption, basically making the same mistake as her predecessor. In her remarks at the conference Empowering Criminal Justice, Ambassador Kim reiterated that the executive order signed by US President Joe Biden on punishing persons who undermine stability in the Western Balkans should act as an impetus to combat corruption in Albania. So far, the ambassador’s approach and efforts have done little to help the cause. To the contrary, her tactic proved counterproductive, creating an impasse within the country’s largest political party, which is also a party in opposition. When a country’s political system is totally corrupt, the top-down approach to combatting corruption does not work; the approach should be from the bottom up, by involving citizens who are mostly innocent victims and who have the real power to change the system—either through their votes or otherwise. Julius Caesar said, “If you break the law, do it to seize power, in all other cases, observe it.”
Getting back to the cyberattack, regardless of who leaked the information or how it was obtained, I am almost certain this illegal act had something to do with the political situation in Albania. The perpetrator was likely hoping that bringing attention to this information would raise public consciousness and thus become an impetus to demand a change and bring the country back onto a democratic track. The perpetrator who released the information could be a disgruntled governmental employee who had access to this information, or a hacker from inside or outside the country. The hacker could be an individual, an organization, or a government.
To understand my conclusion regarding the perpetrator’s motives, it is important to understand the situation in Albania. Although this article is supposed to be about the cyberattack and breach of security in one of the country’s highest governmental institutions, I would like to first provide some relevant background information on the state of democracy in Albania and the “functioning” of the government.
THE FAILED PROMISE OF LIBERAL DEMOCRACY
United Sates President Abraham Lincoln (1809–1865) in one of his speeches during the Civil War, talked about democracy as “government of the people, by the people, for the people.” More than thirty years have passed since the fall of communism in Albania, one of the most brutal and tightly controlled regimes in the world. The collapse of the communist system in Albania was followed by the country’s first multi-party elections, which paved the way for a democratic system and institutions to be established. At the beginning everything was going in the right direction, but not for too long. Cynthia Horne, a transitional justice scholar, wrote in her book Building Trust and Democracy that Albania was the only country in formerly communist Eastern Europe that had laws to deal with the crimes of the communist past, but failed to put them into practice. The political diversion that followed could be attributed to the fact that Albania did not start with a clean slate. Instead, its transition from dictatorship to pluralism happen through the “negotiation and power transfer” model, borrowing this term from Samuel Huntington, one of the founding fathers of the United States. Albania’s newly formed Democratic Party negotiated the transfer of power with the former Communist Party, which became the Socialist Party. The country avoided bloodshed in this manner, which is commendable. However, the communist past continues to haunt Albanian society and hampers its ability to build truly democratic institutions. Some of the most powerful political personalities in government and governmental institutions are disciples of the former regime. Attempts to camouflage their true intentions do not always work because the truth rests not on their claims but on their performance results. There is a Latin saying, “vulpem pilum mutare, non mores,” which translates, “the fox loses his hair, but not his habits.” Altin Gjeta, a research fellow at the Albanian Centre for Good Governance, a Tirana-based NGO, writes the following: “The controversial past has been harnessed politically to manipulate the public discourse with anti-political rhetoric for electoral benefits, and to excuse misconduct in office, corruption, and bad governance. Three decades on, Albania continues to float in a protracted transition to nowhere, still hostage to the ghosts of its communist past that haunt the present—and its future.”
A recent report titled Deconstructing State Capture in Albania: An Examination of Grand Corruption Cases and Tailor-Made Laws from 2008 to 2020, issued jointly by Transparency International and the Institute for Democracy and Mediation, paint a daunting picture of the situation in Albania. Among other things, the report concludes the following:
Grand corruption continues to be fueled by the privatization of the country’s assets and services. This has been enabled by insufficient institutional checks and balances and a politicized public administration that has been sustained by a corrupt judiciary that provides impunity to the perpetrators. The last decade has seen a strengthening of the partnership between politics, business, and organized crime…Government contracts for select businesses with ties to prominent public officials have led to gross mismanagement of public assets, loss of life, and debt incurred by the Albanian taxpayer. The cooperation between political parties, public officials, and organized criminal groups for the purchasing of votes in local and general elections in exchange for favored access to public institutions has severely crippled the integrity of the electoral process…In the case of judicial reform, its slow pace and the vacuum created by the comprehensive vetting of judges and prosecutors have stalled some investigations and prolonged others…The absence of a functioning Constitutional Court and Supreme Court for over two years (2018–2020) has eroded the institutional checks and balances, benefitting illegitimate interests by guaranteeing impunity…Additionally, the most important institution in terms of exercising effective oversight over the executive to ensure that public policy serves public interests—the Albanian Parliament—is not fulfilling its constitutional mandate.
Similarly, another report issued by Transparency International and U4 Anti-Corruption Resource Center, titled Western Balkans and Turkey: Overview of Corruption and Anti-Corruption, claims that “powerful patronage networks have infiltrated and consolidated their control of state institutions. These networks wield influence in many fundamental judiciary, law enforcement, and anti-corruption institutions. As a result, politically independent and effective oversight and prosecution mechanisms can be absent, and corrupt officials and organized criminals can occasionally engage in acts of corruption with impunity. Overall, the region has lost momentum, neither moving forward nor regressing.”
WHY AM I WRITING THIS ARTICLE?
As an Albanian-American born in Montenegro who left the country when I was 20 years old, I remain concerned about the wellbeing of fellow Albanians living in their homelands. I try to remain impartial and unconsumed by politics. However, there are different ways to serve a cause, community, or country, and people do so in the ways that best suit their abilities and characteristics. For me, it is imperative to not remain indifferent on matters of importance, but to express my views and contribute in the best way I can. Watching various talk shows in Tirana, I noted that the pundits in talking about cybersecurity and related topics did not have all the facts straight and were feeding misleading information to the public. I am writing this article to share my perspective on issues at hand. Since the topic is highly technical I am trying to provide the reader with some useful information help understand the public discourse. However, I am mindful that my views are based on personal experiences and practices in the United States, which may or may not conform exactly to those in Albania or Europe.
A FEW WORDS ABOUT CYBERSECURITY AND HACKING
Cybersecurity is quite a complex subject with many technical terms, which outlines measures devised to protect the data stored on computer systems and other electronic devices from bad actors. In contrast, hacking is the process of gaining unauthorized access to such a system or device’s data. To avoid confusion, here are some cybersecurity and hacking definitions in general terms:
- – Hacker: a person who uses their computer skills to gain unauthorized access to (hack) computer systems or networks.
– Cyberattack: any malicious attempt to disrupt, harm, or gain unauthorized control of/access to computer systems, networks, or devices via digital means.
– Data Breach: the unauthorized release of secure, private, or confidential information into the public domain or an untrusted environment. The release can be intentional or unintentional.
– Dark Web: a part of the internet that allows users to remain completely anonymous and untraceable. The dark web is only accessible through specific software and is often used by hackers.
– Nation-State Hacker: a single entity or group that hacks in the interest of their nation’s government, normally to compromise, still, change, or destroy information, or to disrupt other organizations.
– Personally Identifiable Information (PII): any data that can be used to identify an individual, either directly or in conjunction with other forms of data. PII includes but is not limited to names, social security numbers, home addresses, and biometric records.
Data breaches have been around for thousands of years, while hacking is almost as old as the very first computer network. Digital files make life easier for data thieves. According to the internet access provider Private Internet Access (PIA), based on a study from the University of Maryland, computers with internet access experience hacking attempts every 39 seconds. Between January and October 2020, just 730 publicly disclosed breaches exposed more than 22 billion records. Most malicious attackers are financially motivated: 53% of hackers compromise data for monetary gains, while 13% are nation-state hackers and another 13% are “hacktivists.” Nation-state hackers collect information and disrupt other organizations on behalf of an affiliated government. China, Russia, and the United States are three nations that are known to use nation-state attackers. Hacktivists are hackers who gain access to data or disrupt organizations to advance social or political motivations, such as whistleblowers. Although there is a fine line between hacking and whistleblowing, the consequences are different. Hacking is an illegal activity, whereas whistleblowing is a legal activity that constitutes exposing any kind of information or activity that is deemed illegal, unethical, or that constitutes a risk to individuals or the general public. However, if the whistleblower is hacking in order to expose the illegal or unethical activity, does it make the act of hacking more acceptable to our society because it was done to support “the greater good?”
Over the last decade, three huge cybersecurity incidents shook the world:
- – Edward Snowden: former CIA technical assistant who leaked information on the secretive practices of the US National Security Agency (NSA). Though not strictly a “hacking” incident, Snowden exposed American data collection practices that changed the way we think about cybersecurity and online surveillance.
– Julian Assange: creator and owner of WikiLeaks, a website that posts classified documents from non-specified sources, including regarding previously undisclosed war crimes and other government intelligence.
– John Doe: person behind the Panama Papers—the leak that exposed 11.5 million financial and legal records, uncovering a system of offshore accounts and political corruption. The files disclosed practices used by the rich and politically privileged to launder money and avoid taxes.
What happened recently in Albania is nothing new—just another cybersecurity breach, most likely committed by a hacker or whistleblower or both. While the act of hacking is illegal, whistleblowing is not illegal and should be protected. The disclosed information is of outmost importance to Albania because it exposes inherent societal issues that require attention. Investigation of the remuneration anomalies could unmask a system of corruption and illegal activity involving private individuals and governmental officials alike.
WHO IS RESPONSIBLE FOR SECURING PERSONAL DATA?
In recent years, numerous issues have arisen around the way enterprises and governments treat their users’ information. Personal data is processed for political and economic reasons without users’ consent, as happened in the Cambridge Analytica scandal. The whistleblower, Christopher Wylie, revealed a secret relationship between Facebook and a firm called Cambridge Analytica, which harvested data from 87 million Facebook users across the world to target them with political messages without their consent for the purpose of influencing elections.
Cybercrime now presents an important challenge to governments around the world. During a recent G20 Summit, world leaders emphasized the necessity of trust in digital technologies—including consumer protection, intellectual property rights, transparency, and security. Governments are slowly reacting; the European Union is leading user privacy discussions with its General Data Protection Regulations (GDPR), which provide a strong legal foundation. In the United States, privacy laws vary depending on the sector, state, or data type. Meanwhile, technology leaders are pushing for federal privacy laws, and are beginning to see privacy as a human right (World Economic Forum).
Today, there is no consensus on who is responsible for data privacy. Some consumers agree that the responsibility lies with them, but others think governments or businesses are better equipped to deal with this complex issue. According to PricewaterhouseCoopers (PWC), 92% of consumers say companies must be proactive about data protection, 82% agree that the government should regulate how companies use private data, and 72% think that businesses, not the government, are best equipped to protect them.
Many internet users believe they themselves have the ultimate responsibility for their data security. Users should at least take the basic precautions of installing antivirus software, using strong passwords, restricting the amount of information they give out on websites, and opening email only if they know the source. Some users have begun to avoid sharing their information and opting out of various online services. Connected users see the value of data privacy and security, but it is a concern that should be tackled with a combined effort from governments, businesses, and users alike.
WHAT IS CONSIDERED PERSONAL AND CONFIDENTIAL INFORMATION?
To answer this question, I have borrowed from an article posted by Ronald Martinez on DaraHack4fi. The term “confidential information” refers to information to which the general public does not have widespread access. The term “information” means any form of data, including text, images, audio recordings, video clips, proprietary software, and other material that may be available for download from the internet or through an employer’s internal network. There are three types of confidential information: business, proprietary, and personal. Business and proprietary information includes information about customers, sales, marketing, finances, plans, products, technologies, processes, policies, and other information that would be useful to business competitors. Personal information includes government-issued identification numbers, financial records, medical files, and other information that should only be disclosed to individuals with whom you have a legitimate reason to share this information. There are two main ways that information can be kept confidential: physically and electronically. Physical confidentiality can be achieved by keeping documents locked up in a safe or vault. Electronic confidentiality can be achieved by using encryption technology. The goal of confidentiality is to secure data by avoiding unauthorized disclosure of information and only those with valid authorization to access the necessary information should be allowed to do so. This is also known as “need to know” authorization.
The premise is that someone who has obtained confidential information should not use or reveal such information without authorization. Unauthorized use or disclosure of sensitive information may give rise to a breach of confidence lawsuit. There are exceptions, however: an organization or agency may disclose personal information after having obtained a person’s authorization to disclose it for secondary purposes, or if it is required for enforcement-related operations conducted by or on behalf of a law enforcement authority. Furthermore, an organization or agency may disclose personal information if they need to do so in order to investigate or prevent any actual or suspected unlawful activity. When such investigations involve the use of criminal statutes, investigators will follow established procedures to determine whether there is probable cause to believe someone has committed a crime. If so, personal information could be provided to other government agencies responsible for criminal investigations or prosecution.
ARE SALARIES CONFIDENTIAL INFORMATION
In the United States, generally, employee salaries are not considered “confidential information” with some notable exceptions. Under the National Labor Relations Act, employees’ discussion of wages with one another is considered a “concerted activity” that cannot be prohibited under the Act. Additionally, the US Department of Labor recently issued regulations implementing Executive Order 13665, which requires “pay transparency” by federal government contractors. This order generally prohibits contractors from disciplining or firing an employee for asking about wages or sharing wage rate or salary information with others.
Nevertheless, a private-sector employer may restrict managerial employees from discussing wage and salary information with each other. The National Labor Relations Act does not protect managerial employees, and thus their discussion of wages and salaries is not a “concerted activity” protected by that Act. Similarly, the executive order does not apply to private-sector employers (as opposed to federal contractors).
Even in these situations, there may be reasons for employers not to have or enforce a secrecy rule. First, a court may not agree that wages or salaries are properly deemed “confidential” under a non-disclosure agreement or other restrictive covenant signed by an employee or may rule that such an agreement is unenforceable. Second, in some instances, enforcing such a rule may violate other laws concerning wages and pay equality. For example, an employee fired for describing his or her pay to other employees may claim that the employer retaliated against the employee for opposing pay discrepancies between men and women or people of different races (May Law LLP).
WHAT IS PAY TRANSPARENCY AND WHY DOES IT MATTER?
Companies that don’t invest in pay transparency and instead guard information about employee compensation may lose their best people not necessarily because they are underpaying, but because they did not have better communication around compensation. Being more transparent about pay does not have to mean posting everyone’s salary for all to see, though some companies do go that far. What it does mean is that employees will better understand their companies’ compensation philosophies, strategies, and practices. Employees need answers to questions like these: Does the company aim to meet or exceed the market competition when it comes to pay? What compensation data sources does the company use to evaluate the market? What are the salary ranges for all positions at the company? How are raises determined and awarded?
There are different levels of transparency, and each company is going to fall somewhere along a spectrum, but pressure is building for companies to become more transparent with employees about pay. Lately, there has been an incredible amount of media coverage on pay transparency, from the Google employees who created a spreadsheet for workers to share their salaries to a Twitter campaign encouraging people to openly share their current and former salaries. Gravity Payments CEO Don Price cut his own salary to give his employees a much higher basic pay and set the minimum salary at his company to $70,000 per year in an experiment that some describe as lunatic and some others as pioneering. It’s about values, Price said, and hopes others will follow his lead in tackling inequality.
Pay transparency has some other major benefits for both employees and employers. First, pay transparency can help ensure that workers are being paid equitably for equal work. If there are fewer secrets surrounding salaries, it becomes much harder for any pay inequities to arise. That is better for workers in terms of fairness, and it protects employers from potential lawsuits. Even the US government is moving toward better transparency. The Department of Labor recently ruled that federal contractors may not discriminate against workers who discuss pay. Second, pay transparency builds trust. When employees feel valued and are not thinking about whether they might be underpaid, they are more likely to be more fully engaged in their work. Numerous studies have shown that a more engaged workforce leads to better business outcomes. Third, pay transparency increases retention. Companies that are truly committed to retaining and supporting their best employees are going to move in the direction of more transparency. (PayScale’s Compensation Best Practices Report).
The United States government is completely transparent when it comes to government employees pay. The government has established a general schedule (GS) that determines salary ranges for workers in most technical, administrative, clerical, and professional civilian positions. The transparency of the government job pay scale enables job applicants to gain a clear idea of what they can expect to earn. According to the Federal Office of Personnel Management, the GS pay scale determines the pay for a large share of the 1.5 million US government civilian workers worldwide. Compensation ranges are based on the following factors:
- Technical demands of the job
- Educational requirements
- Level of responsibility
- Employee qualifications
The numerous agencies within the government determine the GS level of pay that applies to their job positions. In addition to basic criteria, agencies may choose GS pay levels that make their positions competitive on the broader job market (Federal Resume Guide).
Under open government transparency guidelines, information on public employees (including those employed by federal, state, and municipal governments) is a matter of public record. FederalPay.org has created a powerful search tool that allows public access to the Enterprise Human Resources Integration-Statistical Data Mart (EHRI-SDM) dataset, which contains records for most public employees of the US Federal Government. In addition, there are several sites and search tools that allow the public to check the pay for the president and other members of the executive branch, Congress, and the Supreme Court; see https://pressgallery.house.gov/member-data/salaries.
HOW TO INTERPRET SALARY ANOMALIES IN ALBANIA
Anomalies in pay that cannot be reasonably explained raise questions in any country and should be investigated. When such anomalies happen in a country like Albania, which is riddled with corruption and illicit activities involving government officials, politicians, and unscrupulous business people, the concern is even greater. Most accusations come from politicians themselves, who accuse each other of benefiting from corruption and illicit businesses, including drug trafficking. If such activity does exist in Albania, and all the indications are that it does, a lot of cash would need to be laundered somehow. Cash transactions and real estate investments are quite straightforward, but today there are other more sophisticated techniques involving internet and other non-banking payment systems that allow for money to be moved internationally with ease. Offshore banking was established through legal means to allow for individuals and corporations to avoid paying taxes—but evading taxes is illegal, and offshore banking is now being used for money laundering purposes as well.
Payroll information recently leaked in Albania raises suspicion of a money-laundering scheme that is worth investigating. Such an investigation should be conducted thoroughly and professionally. While it may prove nothing, it may also show that what has already been disclosed was only the tip of the iceberg.
WHAT IS THE RESPONSIBILITY OF GOVERNMENT AGAINST CYBERTHREATS?
Cyberattacks on private sector and government networks have increased considerably both in scale and in scope, as measured by the amount of corporate data stolen or deleted, personally identifiable information compromised, or remediation costs incurred. Cyberthreats are also becoming increasingly more difficult to investigate. Cybercriminals often operate through online media, selling illicit goods and services while operating as legitimate businesses. Many of them are based abroad or shield their identities by using foreign infrastructure, hence cooperation with international law enforcement partners is essential.
The responsibility for defending a nation against any enemy, including from cyberthreats, lies primary with that nation’s government. In the United Sates, the Department of Homeland Security (DHS) is a federal agency designed to protect the country against threats. DHS is a unique agency because after September 11th, 2001, it brought a wide range of responsibilities under one organization—including aviation security, border control, emergency response, and cybersecurity. DHS has a range of cybersecurity mission objectives that include prevention, protection, mitigation, response, and recovery. Through its operation, DHS seeks to assess cybernetic risks and to use its understanding of those risks to promote security and resilience of information communication technology (ICT) systems. DHS collaborates with the information technology (IT) sector to develop and implement improved cybersecurity strategies that could be deployed nationally. During the Obama Administration, DHS was positioned as the lead federal agency for interacting with the private sector on a variety of security matters. However, this does not replace the Federal Bureau of Investigation’s (FBI’s) responsibility for criminal investigation.
In the United States, the FBI has the primary responsibility to investigate crimes across the nation and to work with other intelligence and law enforcement organizations to address the unique set of challenges presented by cyberthreats. However, the information domain on the internet is inherently a different battle space that requires real-time preventive measures. Working in concert with other agencies around the country, the FBI has established a multi-agency Cyber Task Force that brings together the expertise of many stakeholders, as well as the Cyber Action Team (CAT), an elite rapid response force. In a statement before the Senate Armed Services Committee, Scot S. Smith, assistant director, of the FBI’s Cyber Division stated, “CAT members are available to supplement the technical capabilities in the field, and they are typically deployed in support of significant cyber incidents that have the potential to impact public health or safety, national security, economic security, or public confidence.” In addition to these cyber-specific resources, the FBI has other technical assets that can be used as necessary to combat cyberthreats.
Other countries around the world have established integrated systems to protect themselves from different threats, including cyberthreats. Albania does not have the resources to establish such a sophisticated multiprong system—nor does it have to, because Albania’s cyberthreats are minor in comparison to those in developed countries. However, Albania should have an agency that is responsible for cybersecurity that should work in tandem with other international agencies to combat cybercrimes and to protect itself from future threats. Moreover, the government should establish laws to deal with a cyberattack when another one occurs. Calls for members of the government to resign because of the recent unauthorized release of salary information for most of the country’s work force are without merit, provided the government enacts the described security measures to protect against future cyberthreats.